Today we’ll show you how we use data aggregation to evaluate attacks.
Yesterday (September 26, 2023) in the afternoon, apparently the compromised server searched for websites with the PHP web shell “Alpha team shell tesla”, which is used by attackers to control compromised servers without authentication. Next, the attackers searched for “wp-plain.php”, which could be a backdoor.
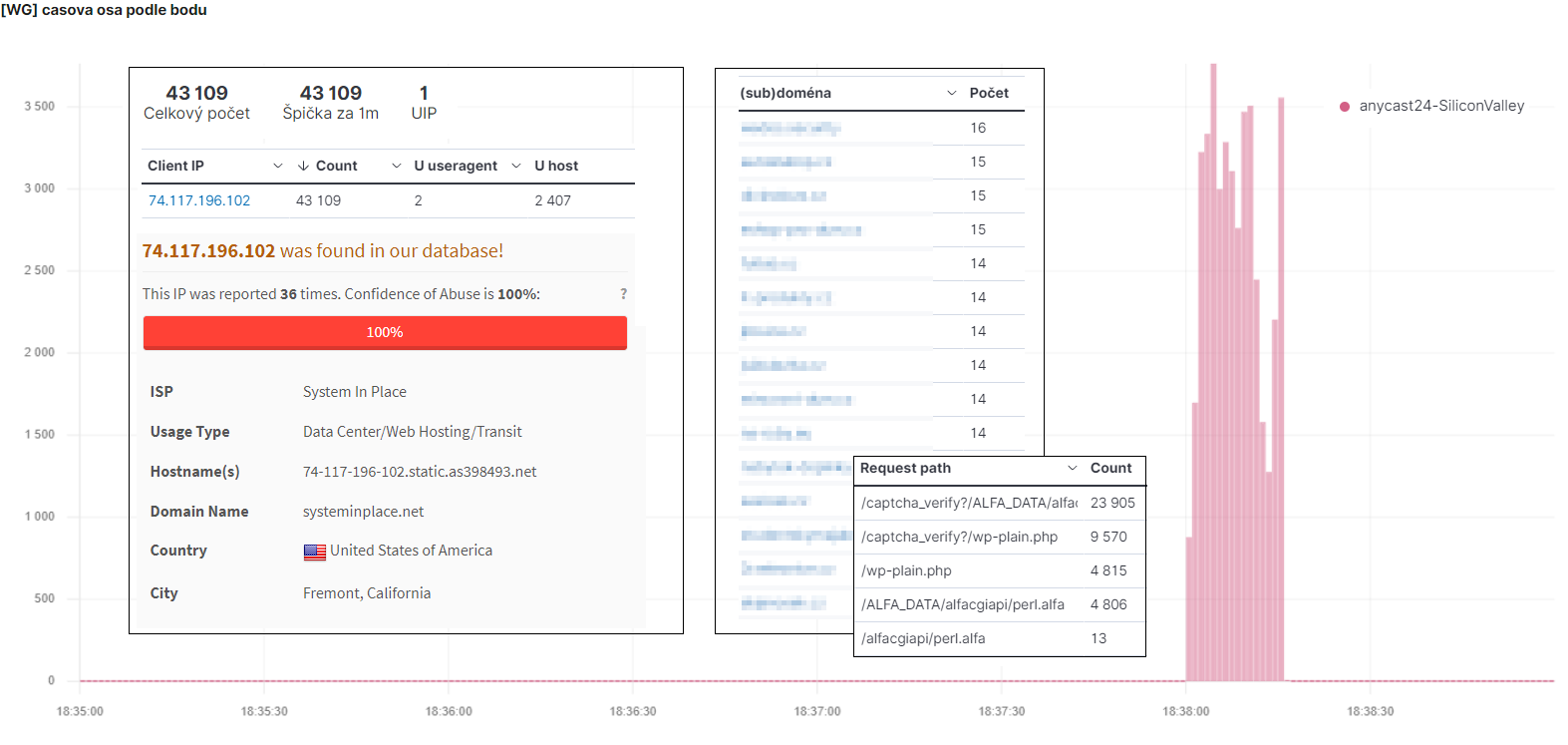
As you can see in the picture they managed to send 43109 requests in 15 seconds. Which we immediately identified as an attack and the vast majority of requests ended up on the captcha. So the attackers quickly gave up, because the websites hidden behind WEDOS Global Protection could no longer be crawled by the bot.

However, we only noticed this by aggregating data from all sites in real time. As you can see in the picture, attackers send only a few requests to each site. For us it was 2 – 16 per domain. Which for 2407 (sub)domains gave a total of 43109.
If you have one website, you have no chance to notice it in the logo, let alone react to it. And there are countless such attacks every day. All of them “eat up” the computing power you pay for, and in the worst case they can discover a vulnerability.
We have a lot of data and we work with it. This includes hundreds of thousands of (sub)domains on our hosting services and thousands protected by WEDOS Global Protection. The more sites WEDOS Global Protection protects, the better, more effective and faster our filters will be. The WEDOS Global infrastructure is an amazing tool not only for protecting websites, but it is the data that makes it so effective.