In October, we mainly tuned the content caching. We have made great progress, especially with WordPress sites. We can return any static content in thousandths of seconds after receiving a request from the user, while checking if it is up-to-date in units of seconds up to 60 seconds (depending on the tariff). The average site on WEDOS Global Protection has increased in speed by approximately 48%.
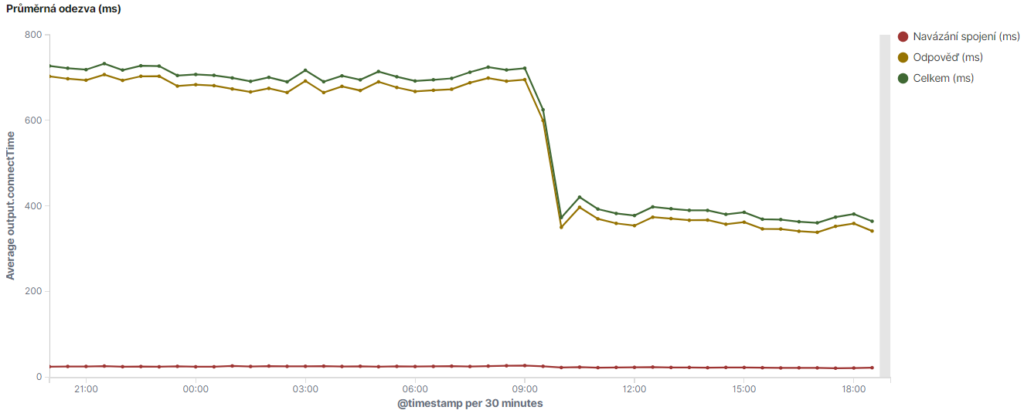
The new cache was launched for all sites on WEDOS Global Protection in early November. Below is a graph of the average response as measured by WEDOS OnLine.
Of course, we’ve been improving the protections as well. Many rules have been revised, we are looking for new methods to be efficient, to help the target server. After all, there are a growing number of customers who do not have hosting directly with us, and there we encounter their rules against attacks. We find that it is common in the Czech Republic to shut down websites with excessive traffic for up to an hour. So we are choosing the appropriate solution to prevent this as well. WEDOS Global Protection can serve as a watchdog for these limits.
Literally every week we find a new use for the WEDOS Global infrastructure.
WEDOS Global
WEDOS Global represents not only an extensive, but above all a cutting-edge infrastructure that is at the forefront of technological advancement. With our global presence spanning thousands of physical servers in dozens of strategically located sites, we are rightly proud of our ability to provide fast, efficient and uncompromisingly reliable services around the world. And we’re just getting started. By the end of the year, more sites will be added and by 2023 we will be over a hundred.
The total connectivity of WEDOS Global currently exceeds 3,000 gigabits per second, which guarantees not only fast, but also secure and seamless data transfer. Our commitment to delivering the best possible service is evident in our careful selection of sites that are not only geographically significant but also have state-of-the-art technical facilities.
The basis is BGP Anycast. This technology allows us to provide faster and more reliable DNS services, which directly contributes to faster website load times and an improved user experience. It also eliminates the greatest force of DDoS attacks because they are dispersed among individual sites where the computing power of thousands of servers can handle them.
New connections (peering)
We are actively expanding our network of WEDOS Global locations (we have several locations lined up). However, it is not easy to find other suitable locations that would allow us to place at least 45 physical servers (as many as we need for computing power) and at the same time offer connectivity of at least 100 Gbps (for fast and stable data transfer even in case of large attacks). When selecting locations for our servers, we limit ourselves to data centers of reputable and verified companies with which we already cooperate.
We are currently focusing on South America, where we still lack a site. Here we encounter mainly obstacles in the form of local legislation.
In the long term, we are considering the establishment of specialized points that would be equipped with hardware components designed for specific purposes (e.g., optimization for specific types of data flows, security, CDN, etc.). Alternatively, we are considering purchasing new extremely powerful servers that could handle the entire site on their own (possibly in pairs). These servers would allow us to cover problem areas more efficiently and quickly.
New link to FICIX (Finland)
On Tuesday 10. On October 2023 at exactly 7:45am, we connected WEDOS Global to the Finnish FICIX internet node, which is significant for customers targeting the Northern European market as it will significantly improve DNS server responsiveness and distribution of cached content from reverse proxies. FICIX is the main internet exchange point in Finland.
New link to BIX.hu (Hungary)
Another important location on the European internet map is Hungary. That’s why we are WEDOS Global 9. On October 2023, they connected to the Budapest Internet Exchange (BIX), which reduced the response time from 30 ms in Hungary to an impressive 6 ms. Reducing response times and increasing DNS stability is part of our plan to become one of the top 5 DNS providers in Europe. We believe that we will achieve this goal in a matter of months. We will then publish the results of the independent measurements.
Would you like to learn more about WEDOS Global?
If you are interested in WEDOS Global and would like to learn more about the advanced technologies we use, we recommend you listen to our presentation from the Kubernetes Community Days Czech & Slovak 2023 conference for a deeper and detailed insight into the technological architecture on which the WEDOS Global infrastructure is built. This expert presentation was led by two colleagues who play a key role in the development of WEDOS Global.
WEDOS Global Protection
WEDOS Global Protection is a prime example of how innovation and technological superiority can propel cybersecurity into a new era. Our service, based on WEDOS Global’s robust and extensive infrastructure, delivers not only protection, but also performance and reliability that exceeds traditional standards.
As a reverse proxy, WEDOS Global Protection is able to perform a wide range of tasks, from filtering incoming attacks, to storing static copies of your site for faster viewing, to masking your real IP address. This is all supported by the latest technologies available for communication with visitors (IPv6, HTTP/3).
WEDOS Global Protection offers a comprehensive package that includes protection against DDoS attacks, a highly effective web firewall, advanced suspicious traffic testing and much more. All without having to change your service provider – just point your domain to our DNS.
For WordPress users, we also have a custom plugin to help you with the whole process. Plus, it makes it easier to identify that you’re using WordPress and set better rules for both protecting and caching content.
WEDOS Global Protection statistics
In October, the number of WEDOS Global Protection users increased to 1,273 (+61) and the total number of protected domains to 5,797 (+776). Among the new users were several who were frequent targets of attacks. Their websites were down for hours. The deployment of WEDOS Global Protection helped them immediately and we received a very enthusiastic response.
Of course, this has had an impact on the number of DDoS attacks recorded. The attackers aren’t going anywhere, they’ll keep coming back and trying again and again. They are looking for new ways and forms of attack to harm you. When they found out they weren’t doing well, they decided to focus on our sites, which wasn’t a good idea. We know our sites and have adapted them to the onslaught and attacks. Actually, it suits us because it gives us valuable information on how to defend our customers.
In October, 3,120,511,662 (-11.29%) requests were recorded out of 8,514,892 (-2.96%) unique IP addresses that were directed to protected domains. On average, the proxy servers handled 100,661,666 requests per day. The drop is due to more efficient filtering of requests before they reach the WAF, where we measure everything, and a change in the form of attacks.

In October, the new HTTP/2 Rapid Reset dominated the L7 DDoS attacks. As soon as the details were released (around October 10, 2023) how it works, it became dominant within days.

L7 DDoS attack HTTP/2 rapid reset
The “HTTP/2 rapid reset” attack is a specific type of cyber attack that exploits the characteristics of the HTTP/2 protocol. This protocol was designed for more efficient and faster data transfer compared to its predecessor HTTP/1.1, through the use of techniques such as request multiplexing, header compression, and other enhancements.
The key aspects of the “HTTP/2 rapid reset” attack are:
- Stream Abuse and Multiplexing: HTTP/2 allows multiplexing, which means that multiple requests can be sent simultaneously over a single TCP connection. An attacker abuses this feature by quickly opening and closing a large number of streams.
- Server Load: This behavior can cause a significant load on the server. The server tries to manage and maintain many open streams, which requires computing power and memory. If this attack is carried out intensively and over a long period of time, the server’s system resources may be exhausted.
- Stream Reset: After opening a stream, the attacker sends a frame RESET signal, which then forces the server to close the stream. Repeatedly sending these signals in rapid succession can cause the server to become overloaded and unavailable to legitimate users.
- Difficult to Detect: Attacks of this type can be difficult to detect because they may appear at first glance to be normal HTTP/2 communications. This requires advanced monitoring and security tools capable of detecting anomalous patterns within HTTP/2 communications.
- Target of attack: This attack typically targets web servers and applications that use HTTP/2, and aims to cause a Denial of Service (DoS) condition where the server is unable to process further legitimate requests.
As HTTP/2 is widely used in modern web applications, it is important that the infrastructure is equipped with adequate security mechanisms to detect and mitigate such attacks.
Or you can use WEDOS Global Protection. WEDOS Global Protection acts as a reverse proxy, meaning that all inbound traffic passes through the infrastructure before reaching the destination server. This architecture enables more efficient traffic filtering and analysis, which is key to detecting and stopping “HTTP/2 rapid reset” attacks. The customer does not have to deal with anything.
The main difference with this attack is that the attacker is not betting on overloading your site for a long time, but on the operator shutting it down. The attacks are so short in order to exceed the limits. We see them mainly targeting sites using various hosted CMS and eCommerce solutions.
What about the other L7 attacks? The statistics mainly reflected new attacks and new customers. A 259.7% increase in HTTP flood looks scary, but it’s only the first seconds to tens of seconds before other protections kick in. Slowloris drop, Connection Exhaustion etc. offsets the significant increase in September. Blocked by the WAF rule are mostly attacks on WordPress and a smaller part of the search for general vulnerabilities.
| L7 DDoS – intercepted by limiting accesses (HTTP flood) | 51 419 767 | +259,70 % |
| L7 DDoS – intercepted problem connections (Slowloris, Connection Exhaustion, etc.) | 2 952 227 | -22,72 % |
| Blocked by WAF rule | 22 916 633 | -12,24 % |
| Further blocking of L7 | 4 770 949 | -22,36 % |

What is an L7 DDoS attack?
L7 A DDoS attack is a type of cyber attack on a website or application that uses common internet requests such as GET and POST. The goal is to slow down or make a web page or an API inaccessible.
Attacks on L7 are difficult to detect and distinguish from normal traffic because they use the same protocols and methods as legitimate users. Special tools and techniques and a thorough analysis of network traffic are needed to eliminate them.
These numbers are just the first attempts at an attack. Once there are repeated attempts that gain momentum (for example, tens of thousands of problem accesses per minute), the IP address goes blacklisted. However, it is more complicated because we treat different IPs differently (for example, a mobile operator gets a JavaScript redirect or a capcha). The same goes for different forms of attacks.

What is a Web Application Firewall (WAF)?
A WAF (Web Application Firewall) is a protection on our reverse proxies that is placed between the attacker and your website. It scans each request in real time, looking for specific signs of an attack or security hole exploitation. If it encounters a suspicious request, it can redirect it to a test (redirect, captcha) or block it.
The stricter protection of WordPress sites using WAF can be seen in the statistics of the largest protected sites. Those that use WordPress have more blocked attacks. However, remember that even if you don’t use WordPress, it doesn’t mean that someone isn’t trying to attack or look for vulnerabilities as if you have WordPress, which puts a strain on the webserver.

When 162,000 unique IPs attack 143,000 websites
On Monday 23. October we experienced the most extensive attack on WordPress installations. It was quite an interesting attack and we wrote a separate article about it.
L3/L4
Of course, our customers are also under classic L3/L4 DDoS attacks. However, in most cases, it’s not worth talking about. Our protections are built for attacks in the hundreds of Gbps. Anything under 10 Gbps doesn’t even send a notification to the technicians. Everything is solved by automatons. In October, the protections were mostly boring. Only one volumetric attack was interesting.

What are L3/L4 attacks?
DDoS attacks at the L3 and L4 layer target the network and transport layers and use a variety of techniques to overwhelm target servers or devices.
Network layer (L3) – provides routing of data between different networks using logical addresses (IP).
Transport layer (L4) – provides reliable and controlled data transfer between endpoints using protocols such as TCP or UDP.
In total we recorded 7 438 (-49.73 %) DDoS attacks. After a busy September, it was rather quiet.

Traditional volumetric DDoS attacks work a little differently. It’s multiple types of attacks at once. So individual attacks can be up to 10 Gbps, but in the end, when it all comes together, you get to tens or hundreds of Gbps. If we take the strongest attack, it comes out as follows:
The strongest DDoS attack was just over 14 Gbps and lasted only a short time. None of the customers noticed anything.

For today’s review, we have also prepared a table of the strongest L3/L4 individual DDoS attacks for October 2023. Attackers usually combine such attacks into one massive one.
| Target | Top Packets/s | Top Bits/s |
|---|---|---|
| Web hosting | 2.6 M | 9.3 G |
| VPS | 2.6 M | 9.0 G |
| VPS | 822.2 k | 9.0 G |
| Infrastructure | 789.3 k | 8.9 G |
| VPS | 787.5 k | 8.8 G |
| VPS | 777.1 k | 8.8 G |
| Dedicated server | 661.4 k | 8.7 G |
| Web hosting | 660.6 k | 8.6 G |
| VPS | 635.5 k | 8.5 G |
| Dedicated server | 632.8 k | 8.4 G |
The most powerful L7 DDoS attacks
Every month we prepare a list of the most powerful and interesting DDoS attacks via L7. We only work with requests that go through to the WAF, i.e. through blacklists and a number of other protections.
1. Attack on wedos.com – peak 2.7M requests per minute
First place this month goes to our website. At the beginning of October came a very short but powerful attack. According to the logs, it lasted less than a minute. Attackers pushed 2.76 million requests from 2,223 UIPs to the WAF and even 2 requests returned 502.
Since then, we’ve made some significant improvements. Firstly, rules on how to better handle these particular attacks and also how to deal with the first onslaught.

- In mid-October, our site was under another major attack with 1.6M requests at the peak of 2,874 UIPs.
2. Attack on e-shop – peak 1.7M requests per minute
In October, we acquired a new customer whose provider was shutting down the site every time it was attacked. We were able to resolve the attacks immediately. However, we were surprised by their strength. For a regular e-shop, an attack with 1.7M requests per minute from 4,174 UIP is really a lot. Just a fraction.

It should be noted that this is a customer the attackers are really trying to get. After many setbacks, they even took on our websites. But these are normally under attack of a larger caliber. The more they try, the more we know about them and the more we continuously improve our protections.
3. Attack on transport company website – peak 1.3M per minute, 7 887 UIP
In October, the ranks of our customers who are under attack and need help fast were extended by a regional city’s transport company. It must be said that the attack on them was one of the more interesting ones. It was comparable to what crashes the websites of big companies, banks and the state in the Czech Republic. Several attacks by pro-Russian hacktivist groups took place in October. However, they didn’t get this website anymore and we didn’t have to limit the connectivity from abroad, on the contrary, we made everything faster thanks to the cache ;).
Before the attackers gave up, they sent 64 million requests out of 7,887 UIPs. At peak it was 1.3M requests per minute.

Bonus – Attack on the municipality website – peak 241K requests per minute
Someone decided to make Saturday afternoon unpleasant for a village in the Hradec Králové Region. Although the attack is not that impressive “only” 241,000 per minute at peak (795,000 requests from 2,240 UIPs), the attack was part of other attacks that also led to their school (another website).

Conclusion
Our WEDOS Global infrastructure is designed to be not only robust but also able to adapt to future challenges. With WEDOS Global, we have not only the vision, but also the real tools and technologies that make us a leader in the provision of Internet services. We are fully aware of our potential to break into the global market and are proud to continue to provide innovative and quality solutions.

