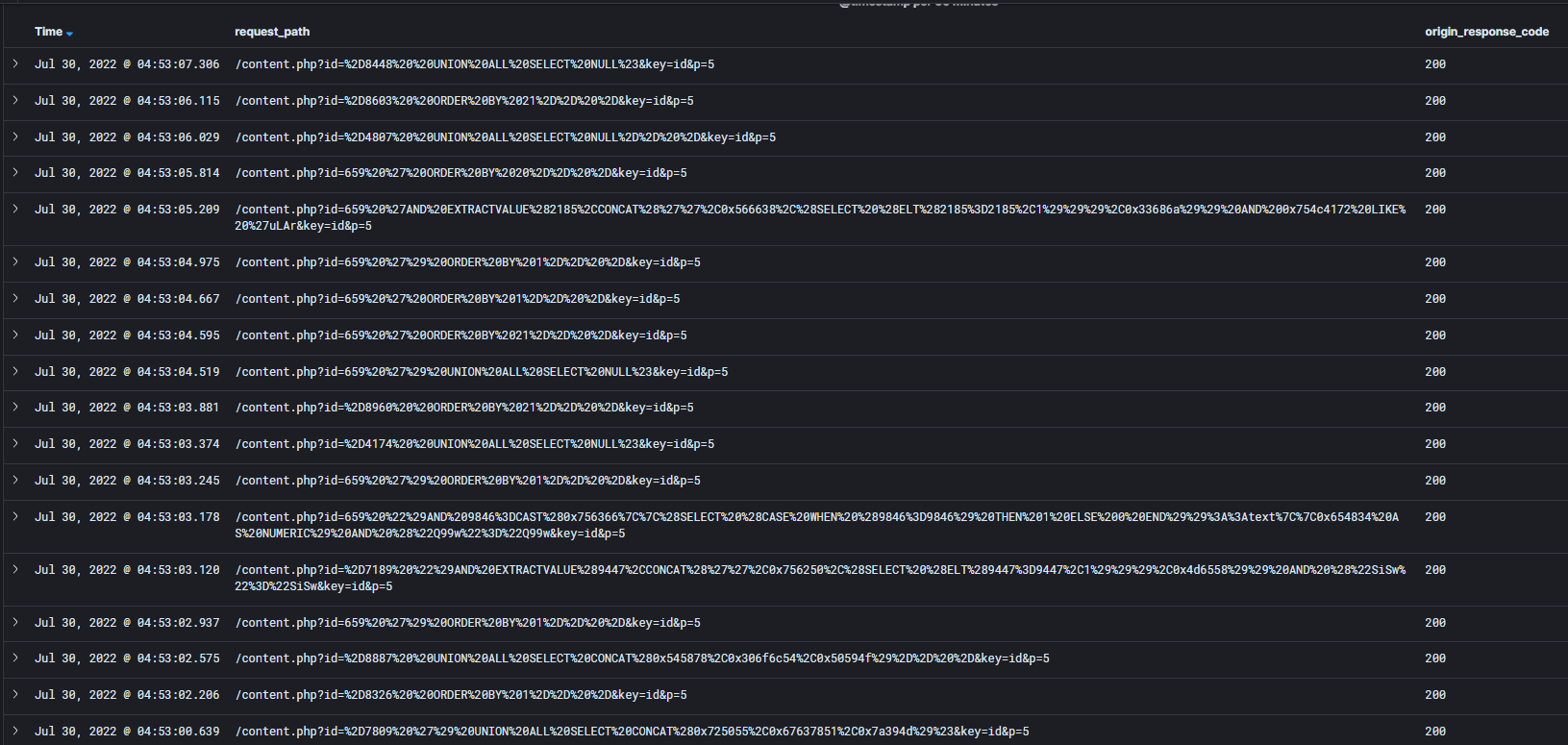
Thanks to central log monitoring, we keep a detailed track of all traffic that goes to our customers’ websites for LowCost, NoLimit, WebSite and WMS services. We can find those under attack very quickly and hide them behind WEDOS Global Protection (if they use our DNS). Most of them are L7 attacks with a large number of requests (someone is simply calling your site with tens to hundreds of thousands of requests per minute). However, the number of SQLi attacks has been increasing in recent days.
Continue reading “We have seen an increase in SQLi attacks in the last few days, how WEDOS Global Protection can help us with this”Building WEDOS Global – New points, centralized sheets and other moonshots
Building a decentralised global network that not only protects us but also allows us to provide entirely new services on it is not only expensive but also quite organisationally and bureaucratically demanding. Definitely one of the biggest challenges we have faced so far.
Continue reading “Building WEDOS Global – New points, centralized sheets and other moonshots”A peek into the WEDOS Global Protection administration
The first service we will launch on our global WEDOS Global network will be WEDOS Global Protection. It has an important task – to protect all our customers’ websites from various types of attacks and our infrastructure at the same time. Over time, we will make the WEDOS Global Protection administration available to everyone so that they can adjust the protection settings to their liking.
Continue reading “A peek into the WEDOS Global Protection administration”The ongoing cyber war may affect you too, get ready for it!
We publicly condemn the invasion of Ukraine by Russian armed forces, which is currently accompanied by strong cyber-attacks by Russia.
The current war is not only a war of arms, but it is also a cyber war that can affect you. We have made the following key recommendations:
Continue reading “The ongoing cyber war may affect you too, get ready for it!”Two more examples of application layer attacks on our customers
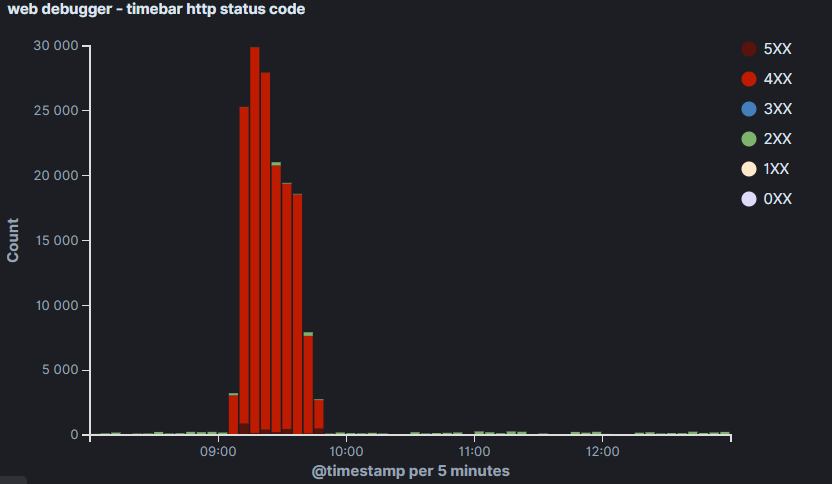
Last month, we showed you in the article “DDoS extortion cases on the application layer are starting to appear ” how the extortion and subsequent DDoS attack on a customer’s website takes place. We know that these cases are gradually increasing, but the pace is accelerating unpleasantly. In addition, we can see from the analysis of logs that attackers are trying to mask their attacks better, trying new methods and looking for the limits of protection.
Continue reading “Two more examples of application layer attacks on our customers”Cases of application layer DDoS extortion are beginning to emerge
Extortion by DDoS attack is nothing new. Large botnets can carry out a fairly powerful attack nowadays, which can easily clog several 100 Gbps routes(we have already seen this happen). Fortunately, they are relatively rare because they are expensive. Medium attacks (above 10 Gbps) are encountered more frequently (even several times a month). And smaller ones (under 10 Gbps) are almost a daily occurrence. However, this classical kind of brute force attack (in terms of data volume or packet count) is relatively well detected and filtered. It is worse with application layer attacks, such as those that try to pass themselves off as normal traffic.
Continue reading “Cases of application layer DDoS extortion are beginning to emerge”